If you know anything about HIPAA, it’s that it requires Protected Health Information (PHI) to be kept private and secure. But ensuring HIPAA compliance relies on you—and your staff—knowing what exactly qualifies as PHI.
Some team members tend to think everything is PHI, while others think only diagnosis information is PHI—but this is one situation in which clarity is critical. You can’t afford confusion, as the Office for Civil Rights (OCR), the enforcement department for HIPAA compliance, won’t accept ignorance as an excuse for HIPAA violations.
Today, we’re going back to the basics and covering what specifically counts as PHI—as we’re calling it, the ABCs of PHI. Ready? Let’s jump in.
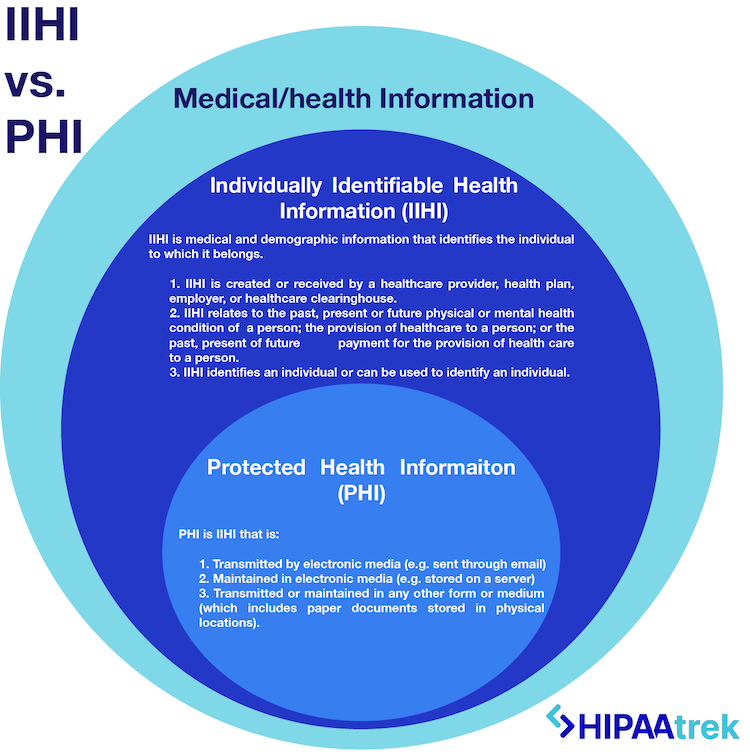
What is Individually Identifiable Health Information?
To begin understanding PHI, we need to start with IIHI, the category that PHI falls within. Individually Identifiable Health Information (IIHI) goes beyond medical information about a person to include their demographics. IIHI meets these conditions:
- Is created or received by a healthcare provider, health plan, employer, or healthcare clearinghouse.
- Relates to the past, present, or future physical/mental health or condition of a person; the provision of health care to a person; or the past, present or future payment for the provision of health care to a person.
- Identifies an individual or can be used to identify an individual.
In short, IIHI is medical information that identifies the individual to which it belongs.
What is Protected Health Information Under HIPAA?
According to HIPAA, Protected Health Information includes IIHI that is:
- Transmitted by electronic media (e.g. sent through email),
- Maintained in electronic media (e.g. stored on a server), or
- Transmitted or maintained in any other form or medium (including paper documents stored in physical locations).
All PHI is IIHI, but not all IIHI is PHI. This is because HIPAA does not protect all individually identifiable health information. The IIHI has to be transmitted or maintained in some form to be protected, qualifying it as PHI.

HIPAA Protected Health Information Identifiers
Wondering what exactly makes information identifiable? According to HIPAA, there are 18 identifiers that make medical information identifiable:
- Names (full name or last name and initial)
- All geographic subdivisions smaller than a State, including street address, city, county, precinct, zip code, and their equivalent geocodes, except for the initial three digits of a zip code if, according to the current publicly available data from the Bureau of the Census:
- The geographic unit formed by combining all zip codes with the same three initial digits contains more than 20,000 people, and
- The initial three digits of a zip code for all such geographic units containing 20,000 or fewer people is changed to 000.
- All elements of dates (except year) for dates directly related to an individual, including birth date, admission date, discharge date, and date of death. This includes all ages over 89 and all elements of dates (including year) indicative of such age, except that such ages and elements may be aggregated into a single category of age 90 or older.
- Telephone numbers
- Fax numbers
- Email addresses
- Social Security Numbers
- Medical record numbers
- Health plan beneficiary numbers
- Account numbers
- Certificate/license numbers
- Vehicle identifiers, such as serial numbers and license plate numbers
- Device identifiers and serial numbers
- Web Universal Resource Locators (URLs)
- Internet Protocol (IP) address numbers
- Biometric identifiers, including finger, retinal, and voice prints
- Full face photos and any comparable images
- Any other unique identifying number, characteristic, or code
When these identifiers can be used in combination with other health information to identify an individual, it qualifies as PHI under HIPAA. Consequently, if these identifiers are not present, the information is not identifiable. If you remove all identifiers, you have de-identified the information, meaning it is no longer PHI.
READ MORE: When Can I Disclose PHI?
Examples of PHI
In each of the following scenarios, both medical information and at least one identifying piece of information are present, making the medical information PHI:
PHI Scenario One: You work at the dentist’s office. You open an email attachment that lists the patients scheduled for next week. You see their first and last names, phone numbers, appointment dates, and expected procedures. This email attachment is PHI because it contains three identifiers (names, appointment dates, phone numbers) and medical information (expected procedures).
PHI Scenario Two: As a patient, you walk into a clinic and see reports lying on the reception desk. You can see patients’ lab test results with their names and dates of birth. These reports are PHI because there is identifying information (names and DOBs) alongside the medical information (lab results). The clinic has also violated HIPAA by leaving PHI in plain view.
Examples That Are Not PHI
The following is not IIHI or PHI because no identifiers are attached to medical information or vice versa, making it impossible to identify the person:
Non-PHI Scenario One: You walk out of a hospital and find a piece of paper on the ground with a person’s name and admission date on it. These are two identifiers. However, the paper isn’t PHI because it doesn’t list the name of a hospital and may not represent a person’s medical treatment. The paper could’ve come from anyone, and the “admission date” could refer to many things besides hospital admission.
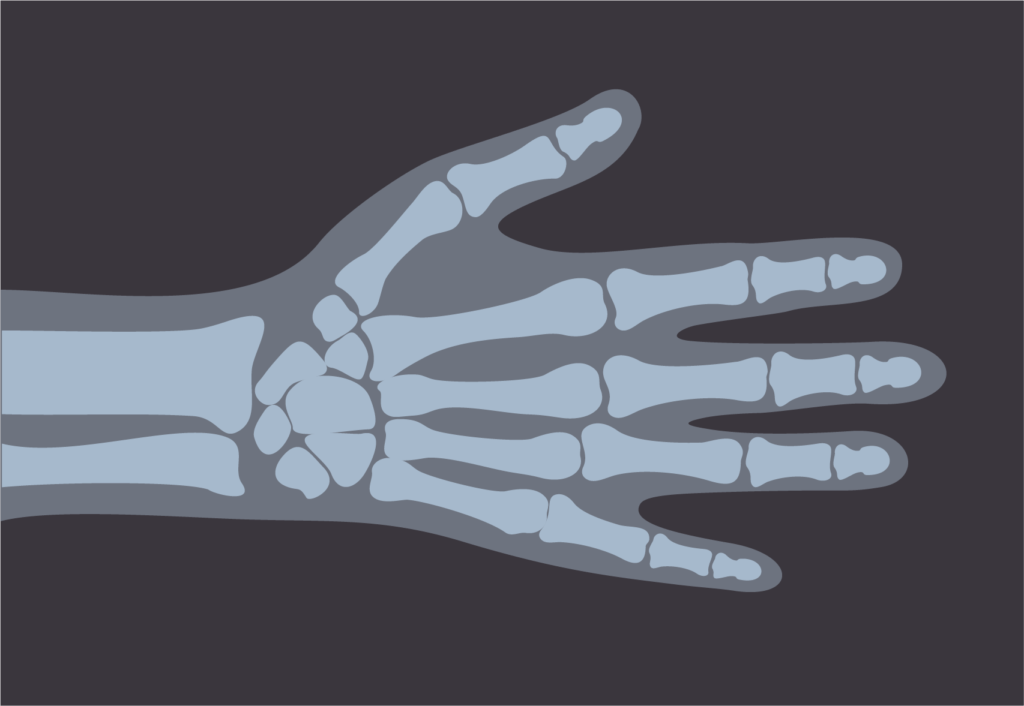
Non-PHI Scenario Two: In the radiology department, you come across an X-ray of a hand. However, no information is attached to the image, making it impossible to know to whom it belongs. Therefore, the X-ray is not PHI; it is simply medical information.
Managing PHI Under HIPAA
An accurate understanding of what is and is not Protected Health Information (PHI) under HIPAA—for both you and your staff—is critical to the foundation of your compliance program.
The specifics of what qualifies as PHI (as well as what is not PHI) should be reinforced regularly to ensure this information is kept private and secure by your team. Employee training should educate the team on this information, and posters and email reminders can be used to reinforce the details to ensure compliance.
Need More Guidance? Grab Our PHI Decision Tree!
This simple cheat sheet makes it easy to recognize when you’re interacting with protected health information.
HIPAAtrek is an all-in-one HIPAA compliance software that helps you manage every aspect of your compliance—including the policies and trainings defining Protected Health Information (PHI)—while tracking each step you take to build proof of your compliance efforts.