In 2019, 764 healthcare providers were hit with ransomware. These organizations temporarily or permanently lost their medical records, had to redirect patients or cancel non-emergency procedures, and some even closed their doors for good.
According to an Emsisoft report, the average ransomware incident costs $8.1 million and 287 days to recover. Besides monetary damage, ransomware attacks disrupt patient care. “The fact that there were no confirmed ransomware-related deaths in 2019 is simply due to good luck,” said Fabian Wosar, CTO of Emsisoft, “and that luck may not continue into 2020.”
Let’s take a step back to examine what ransomware is, why healthcare organizations are common targets for hackers, examples of ransomware attacks across different organization types, and how you can defend your organization against this malware.
What is Ransomware?
Ransomware is a type of malware that attempts to deny access to a user’s data, usually by encrypting the data with a key known only to the hacker who deployed the malware, until a ransom is paid. The ransomware may also destroy or exfiltrate its victim’s data.
Some of the common ransomware we saw in 2019 include:
- WannaCry
- Ryuk
- NotPetya
- Jigsaw
- SamSam
- Maze
- And many more
Why are Healthcare Organizations Popular Targets for Hackers?
Healthcare is a common target because the data these organizations hold is so critical that they are more likely to pay the ransom to regain access to it. In other words, it’s a quick win for the hacker.
Hackers often find success at healthcare organizations because many providers don’t prioritize cybersecurity as they ought to. They fall prey because:
- They don’t have a proper security policy plan or disaster recovery plan in place
- They fail to perform risk assessments
- They don’t train their staff on security best practices
- They don’t encrypt their data
These negligent cybersecurity practices leave the door wide open for ransomware to take over.
Ransomware in Action: 2019
If you think hackers only target large hospital systems and government agencies, think again. Last year, we saw attacks on healthcare practices of all sizes, from clinics to hospital systems to IT vendors.
Let’s look at some examples:
Vendor
In November 2019, Complete Technology Solutions, an IT service vendor for dental practices, was hit with Sodinokibi (or rEvil) ransomware, which spread to at least 100 of CTS’s clients. The hackers compromised a remote-control admin tool that the vendor used to configure clients’ offices.
CTS didn’t pay the $700,000 ransom to unlock their infected systems. As a result, many of their clients independently attempted to regain access to their own data. Some of these dental offices had to turn away patients as a result of the malware attack.
Small Practice
The cost of recovering from a ransomware attack can devastate small practices. Brookside ENT and Hearing Center, a two-doctor Michigan medical practice, permanently shut down after a ransomware attack that locked down their medical records, billing and scheduling functions, and more. Instead of paying the ransom or recovering the data, the doctors retired early, leaving their patients’ data in the hackers’ hands.
Hospital System
In October 2019, Alabama hospital group DCH Health Systems paid the ransom and purchased the decryption keys from a hacker in order to regain access to their locked systems and encrypted files. The three hospitals had to use paper records for a week and were forced to turn non-emergency patients away.
DCH did have backup files, which allowed them to restore certain components of their system. Without these backups, the devastation from this ransomware attack would’ve been much worse.
How Do I Protect My Organization from Ransomware?
Clearly, ransomware is a growing threat to healthcare organizations, and you are not immune! There are three steps to thoroughly prepare your organization to face malware attacks: Prevent, Respond, and Recover.
Preventing Ransomware
To prevent ransomware, you need to make sure the following technical safeguards are in place:
- A security risk analysis and security management process
- Intrusion detection systems and monitoring apps
- Access controls, which limit data access to only those who are authorized
- Data backups and restoration testing to ensure operations can continue after an attack
- Virus protection software, firewalls, and email filters
- Frequent patch updating on apps, operating systems, and software
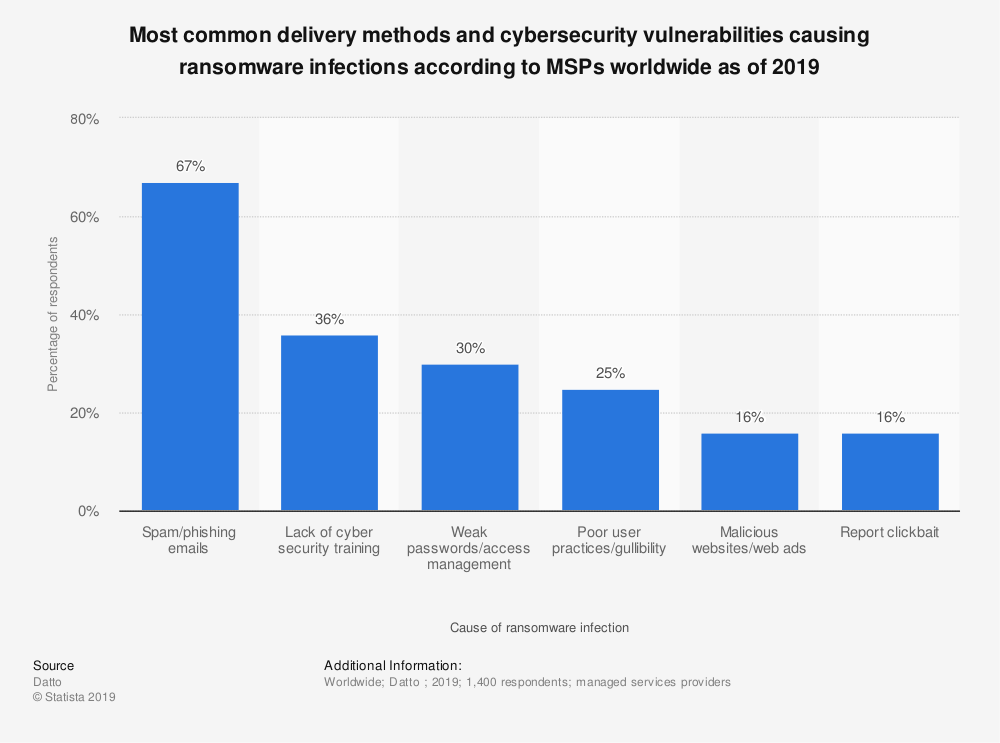
Make sure you train your team on recognizing attempted ransomware attacks. They should know that links in emails, ZIP file attachments, and malicious URLs are all potential methods hackers use to deliver ransomware to a user’s computer.
Hackers are also able to display the lock symbol in your browser, which can deceive even the most alert employees. They are also increasingly using Microsoft file sharing to look legitimate.
Responding to Ransomware
You need to have a ransomware response plan so that everyone is ready to handle an attack. A response plan has several steps:
- Once you know an attack is underway, you’ll need to conduct an initial analysis. Ask yourself:
- Is it a known malware?
- What are the algorithmic steps undertaken by the malware?
- What are the characteristics of the attack?
- Where did the attack originate?
- What are the industry recommendations for this type of malware?
In this initial step, make sure you contact your local police department and regional FBI office, so they can respond to the attack as well.
- The next step is to contain the impact and propagation of the malware. What systems or hardware have been impacted? What systems should be taken off the network to prevent further spreading?
- The last step is to eradicate the malware. This may involve removal solutions, wiping your machines, or even paying the ransom.
Once you have a ransomware response plan, practice carrying it out. All workforce members should understand their role and be ready to put it into practice at a moment’s notice.
Recovering from Ransomware
After an attack, you’ll need to restore lost data. If you have non-infected or off-line backups (which you should), you will restore this data. You will also reconnect systems that were taken offline during the response protocol. If there are apps or systems that can’t be cleaned of the malware, permanently remove them.
Breach Risk Assessment
When your data has been locked down in a ransomware attack, the security or privacy of the data has most likely been compromised, even if you paid the ransom or restored the data. You have to assume the attack resulted in a data breach.
Therefore, the last step is to conduct a breach risk assessment. This helps you assess the risk that your electronic data was actually compromised in the attack.
In Summary
As hackers are becoming more and more sophisticated, you can’t afford to leave security up to chance. It’s your responsibility to keep your patients’ data private and secure. Therefore, be ready to prevent an attack, respond to an attack, and recover from an attack.
Make sure your cybersecurity practices are ahead of the curve and your entire team knows how to recognize an attempted attack. You also need to put into place a ransomware response plan and practice carrying it out.
Check out our Breach Notification Letter Template!
Our free template makes it simple to create a compliant breach notification.













